Increased Cybersecurity concerns, threats, and the steps to prevent these are the biggest dilemma among government bodies and organizations throughout the globe. No matter how secure the functionalities are, there are always chances of small loopholes that can be misused, thereby resulting in loss or misuse of important data. Well Post Covid-19,
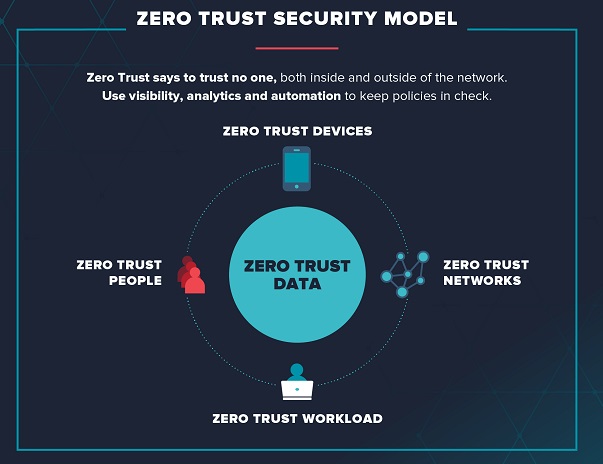
Digital Transformation has to be the need of the hour considering the reign of cashless transactions, zero contact communication, and all those preventing physical contact. Zero Trust is a security concept that requires all users, even those inside the organization’s enterprise network, to be authenticated, authorized, and continuously validating security configuration and posture, before being granted or keeping access to applications and data. IEEE is the world’s largest technical professional organization dedicated to advancing technology for the benefit of humanity to inspire a global community through its highly cited publications, conferences, technology standards, and professional and educational activities. ELE Times’s Correspondent Mannu Mathew spoke with Bala Prasad Peddigari, Senior IEEE Member, to know more about the need for Zero-Trust Model in today’s digital era:
Following are the excerpts of the conversation:

ELE Times: With the world progressively transforming from Analog to Digital, how efficient, and strong is the cyber world today in terms of protection and security?
Bala Prasad: We are living in times of transformation; our organizations are moving physical assets online; digitalization is taking over the globe and data is becoming the new oil to monetize further. Inevitably, we are also witnessing a plethora of challenges with digital adoption and one of the grueling challenges is cybersecurity as digital opens many vulnerabilities to deal with. As per a recent IEEE survey of CIOs and CTOs, the top two concerns for CIOs and CTOs when it comes to the cybersecurity of their organization are – managing privacy issues related to the mobile workforce including employees bringing their own devices to work and managing the security issues associated to the device economy of the enterprises. This is not surprising, since the number of connected devices such as smartphones, tablets, sensors, robots, and drones is increasing dramatically. Slightly more than one-third (34%) of CIO and CTO respondents said they can track and manage 26-50% of devices connected to their business, while 20% of those surveyed said they could track and manage 51-75% of connected devices. As the attack surface has increased significantly, cybersecurity concerns have also grown. There are more points of vulnerability in the digital ecosystem and the sheer volumes pose an additional challenge.
However, data breaches can be prevented by ensuring rigorous enforcement of the security policy in an organization and its partners by ensuring adequate training and awareness on security policies and procedures. Further, employing the Défense in Depth strategy can help in identifying, mitigating, and eliminating cyber-attacks from the overall equation. Today, organizations are deploying security tools to continuously monitor and protect their workload, end-points, and data through encryption, access control lists, security alerts. Continuous risk assessment audits and data security testing is a parallel activity that will help organizations proactively identify and plug gaps, thus securing data. If a data breach occurs, mitigation actions begin with containing further breach by taking systems offline and limiting further access, fixing the vulnerability, analyzing the damage for initiating reparative actions, reaching out to the affected parties with clear messages, contacting online sites to scrub off leaked data, initiating an audit and conducting data security tests.
ELE Times: Please comment on the Indian market and the apprehensions in terms of achieving a secure and reliable digital atmosphere.
Bala Prasad: According to the India Cybersecurity Services Landscape report by the Data Security Council of India (DSCI), the size of the Indian cybersecurity services industry is expected to grow from $4.3 billion in 2019-20 to $7.6 billion in 2022. Cloud, Identity and Access Management, Big Data Analytics, and Data Security have been getting the most traction so far, but the next generation of cybersecurity offerings will revolve around Blockchain, Quantum Cryptography, and IoT.
According to a recent report titled, “Excellence in Risk Management India 2021, Spotlight on Resilience: Risk management during COVID-19,” published by global insurance broker Marsh and Risk management society RIMS, Indian companies are also innovating in cybersecurity with 50-55% of them being involved in the creation of the IP (intellectual property) and 45% of them having R&D security labs. Around 50% of companies are taking advantage of AI (Artificial Intelligence) to improve their cyber services. Over 35% of companies are re-skilling half of their security workforce, while 60% of them are giving more priority to the hiring of skilled talent for running security operations.
Sensors and devices, apps, the internet, and cloud computing are the main building blocks of this digital age. Each block presents a point of weakness. While the cloud and internet are core infrastructure prone to Distributed Denial of Service (DDoS) attacks, there is a greater focus on cybersecurity by service providers due to mission criticality. Vulnerabilities due to human beings, both inadvertent and intentional – are more challenging to defend. While installation of reputed anti-malware/anti-virus/anti-ransomware software on end devices is essential, it is equally important to raise the awareness of each digital citizen on cybersecurity practices.
ELE Times: Explain the functioning in a zero-trust model network.
Bala Prasad: I’ll explain the network with the help of a BFSI example. Many banks have adopted a zero-trust security architecture. In the process, they have established Défense in Depth Security strategy across the organization by strengthening the systems through secure access. Through multi-factor authentication and deploying the access control lists to authorize the right level of access is given to establish trust following the security policies of the organization. Added to multifactor authentication of users, users are authorized based on verification of the location of access, specific device, type of transaction, etc. Further, they seek to increase awareness of cyber threats and safe cyber practices by sending constant reminders via emails, automated calls, and text messages.
Measures at the customer end are constantly evolving as new threats emerge. Thus, adopting a zero-trust security architecture could help manage cybersecurity incidents by the reduction in the attack surface. This multi-layer approach would entail new security protocols that every digital citizen should embrace, even if slightly inconvenient. For. e.g., a user may not get blanket access to all features and functions in a system. The principle of least privilege would be used to assign user rights. Hence, further transactions after secure access into a system may require more authentication.
ELE Times: Comment on the future and highlight the innovations involved in the cyber world.
Bala Prasad: As we all know, cybersecurity is a hygiene factor in the digital world. While one tends to think of technology trends, the fact remains that cybersecurity solutions constantly need to predict and do better to meet the goals of a cyber proof future. Artificial Intelligence (AI), the technology that is in the limelight, is a great tool for cybersecurity products. AI can be used to quickly process different transactional behaviors and trigger actions. They would help decision making as well as reduce response time to threats. However, it is a constant cat-and-mouse game as new cybersecurity solutions emerge, and cyber criminals breach it. Hence, cybercriminals are likely to use AI to beat cyber defenses that leverage Artificial Intelligence. Security process automation and quantum cryptography are other emerging areas that could significantly enhance cybersecurity. Let us investigate some of these technologies which are converging to change the cyber landscape and its future:
- Big Data: Growing volumes of data and metadata triggering the importance of data lineage
- Edge Computing: Higher adoption of APIs are exposing edge devices to be infected through Bad Bots
- Artificial Intelligence and Intelligent Assistants: AI automated cyberattacks and personalized spear-phishing attacks through Intelligent Assistants are becoming prominent
- IoT and Blockchain: Endpoints are exploited through botnets to hijack secure keys and devices
- Quantum Computing: Increase in compute capacity enabling the standardization toward post-quantum cryptography
- 5G: Explosion of devices and needs triggering the need to adopt network slicing and enable security levers across multiple logical networks across the shared physical network
- Cloud: Establishing the trust with the right identity-making identity to be a new perimeter across the cloud
Cloud has become the new epicenter of cybersecurity and it is opening future innovations, driving new opportunities in the area of:
- Real-time Behavioural monitoring: Many new-age digital enterprises are building the security software to support Cyber Défense using AI to deliver endpoint protection, workload protection, container protection, Intrusion detection, security-events correlations, vulnerability management, and malware detection and analysis
- Actionable insights powered by the confluence of Artificial Intelligence, Machine Learning, GPU-based compute power, Data Science, and Analytics: Many new opportunities are emerging to strengthen the overall protection against cybercrime through AI through Digital Forensics, image/audio/video analytics, and video-based surveillance, and identification
- 5G and IoT are leveraged for securing the Connected Future: This is helping in building resilient systems, new trust models, context-aware smarter AI powering devices, improved decision cycle time
In short, organizations need to embrace future innovations by considering a cross-layer approach to security and protect communication paths between devices, users, and the core network. The key to a cyber-safe future lies in educating every digital neophyte on essential cybersecurity practices during initiation itself. This is akin to teaching road safety to children. Additionally, verify before trust should be the motto – whether for system interactions or personal transactions. Ultimately, the idiom – “If it is too good to be true, it probably is” stands re-enforced.
Related Links: How prepared is the future for implementing security in a Multi-Cloud Environment