The transition to autonomous driving and public concerns about driverless vehicles’ safety is making cybersecurity a top priority for automobile original equipment manufacturers (OEMs). The integrity of vehicle systems and the control of the vehicle must be safeguarded to ensure the safety of drivers, passengers, and pedestrians. While the need for cybersecurity in areas like vehicle subsystems connected via networks is evident, it is equally crucial for image sensors used in advanced driver assistance systems (ADAS) and driver monitoring.
Image sensors serve as the eyes of the vehicle, enabling ADAS functions, such as lane departure warnings, pedestrian detection, and emergency braking. They help vehicle systems with assessing the surroundings and monitoring driver behavior. In the future, they will assist with identifying and authenticating the car’s users and monitor their vital signs to enable the onboard computer to assume control if the driver becomes incapacitated. Therefore, image sensors must remain functional, especially in the extreme situations that an automobile can encounter.
Cybersecurity threats
There are four main cybersecurity threats to consider about automotive image sensors: counterfeiting, tampering, bypassing, and eavesdropping (for in-cabin in particular).
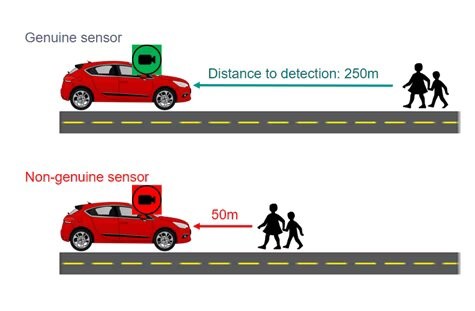
Counterfeiting is on the rise due to the components shortages in the automotive semiconductor industry. While a non-genuine part may not be fitted with malicious intent, it can jeopardize system performance. At best, the ADAS system won’t work at all with the non-genuine part because of different startup sequences, protocols, firmware and software. In the worst scenario, the system uses the substandard part with severely degraded performances that compromise the system’s safety features.
An Automatic Emergency Braking (AEB) system operates on the assumption that its image sensors have specific characteristics (high dynamic range, low light performance) and are calibrated to these specifications (exposure control, frame per second (fps)). The counterfeit sensor may look identical to the original, but its performance and characteristics can differ significantly. For example, a counterfeit camera might use the same sensor but may not have been tested to ensure the final assembly meets performance specifications, which could be a symptom like a failure at the high end of the operating range. So it appears to work in average conditions but degrades or simply fails in other conditions such as hot, sunny days or cold winter nights. If a counterfeit were really sophisticated, it might mimic the real sensor for initialization or simple health checks but deliver dramatically lower performance, either in dynamic range or in frame rate. Since the AEB system is optimized with the genuine part, the degraded performance of the counterfeit replacement will also alter the system’s performance – with potentially tragic consequences. Objects or pedestrians that could be detected a longer distance in front of the car, leaving seconds of time to react, may now only be detected within a few meters and insufficient time to avoid collision (Figure 1).
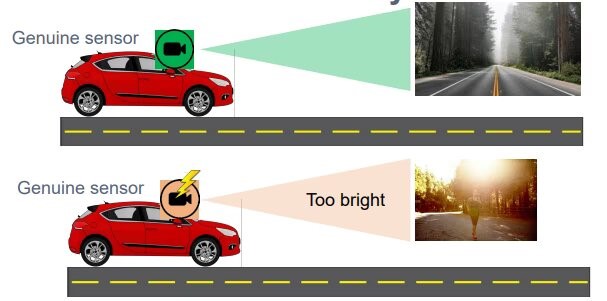
Tampering with the image sensor configuration can also compromise its performance. A vehicle’s system is programmed to configure the image sensor to optimize the image quality for the machine vision algorithms qualified and tested for the specific implementation. However, the performance can be compromised if someone (or something) modifies that configuration. It may no longer be possible to guarantee that the scene facing the car is perceived correctly by the vehicle system (Figure 2).
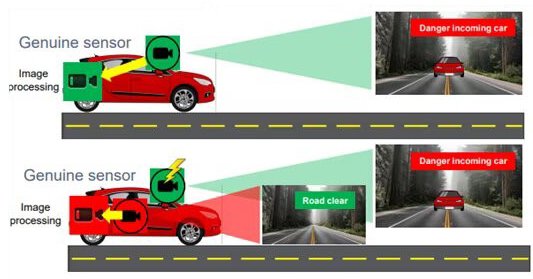
Bypassing an image sensor entirely can render the vehicle blind, preventing the detection of potential hazards. An image sensor provides the image processor with raw video data, which is used to extract critical information about front-facing obstacles so that the car can respond appropriately. For example, the system receiving raw video data from the sensor can detect an approaching vehicle and decide to use the brakes or steer the car away from the hazard (whichever is the safest action). If the image sensor has been bypassed, the system is no longer receiving raw video data and it may not detect the approaching vehicle at all (Figure 3).
Ensuring compliance
In 2021 the United Nations Economic Commission for Europe (UNECE) working group released the UN-R155, a regulation on cybersecurity by mandating OEMs to put in place a Cybersecurity Management System (CSMS). This regulation has been binding since July 2022 to address these rising threats. Automotive suppliers must ensure that all the relevant components comply with the ISO 21434 cybersecurity standard. While using ISO 21434-compliant parts alone is not sufficient to be UNECE compliant, it is a key part of achieving that compliance.
onsemi began implementing cybersecurity features in selected ADAS image sensors in 2018 to make them cybersecurity ready, and those sensors are on track to be cybersecurity compliant by 2024. The authentication feature allows onsemi image sensors to prove to the host that they are genuine. This is achieved by using a certificate chain or a pre-shared key. To ensure video data integrity, a message authentication code (or MAC) is used to prove that a video data stream has not been tampered with between the sensor and the host. Finally, sensor control and configuration data are protected against tampering with specific key registers using MACs. Because tampering mitigation protocol varies among systems, the system processor will be the ultimate decision-maker in the case of tempering detection.
In summary, cybersecurity compliance is vital to prevent automotive image sensors from becoming the Trojan horses of complex automotive electronics systems. For OEMs, compliance requires more than the cybersecurity control circuits in the image sensor. But having cyber-secured image sensors is a fundamental requirement for enabling ADAS and in-cabin monitoring systems achieving full cybersecurity compliance.